Why Business Continuity Planning Matters More Than Ever Downtime is more than an inconvenience; it's a threat to your bottom line. For small and midsize businesses (SMBs) in Southern California, a single IT...

Our smartphones accompany us everywhere, holding sensitive information like passwords and confidential business chats. Yet, the alarming reality is that phone tracking is surprisingly widespread and easier to execute...
Key Takeaways Email is still the #1 attack vector for cybercriminals—and small businesses are prime targets. Standard cloud email solutions are not enough to block modern threats like phishing,...

Many small business owners mistakenly believe that regulatory compliance concerns only large corporations. However, in 2025, that assumption is far from accurate. With regulations tightening across industries, small...
Key Takeaways Inland Empire SMBs face rising threats from BEC scams, ransomware, remote access vulnerabilities, insider risks, and AI-powered phishing. Small businesses are no longer flying under the...

You've probably heard the phrase: You get what you pay for. This is especially true in the world of IT. At first glance, opting for a low-cost managed IT service might look like a smart move—lower monthly...

Key Takeaways Offshore IT support may cut costs but introduces delays, miscommunication, and real data security risks. Local IT support offers faster responses, clearer communication, and deeper...

Key Takeaways Layered cybersecurity (like a castle's defenses) is essential in today's threat landscape. Zero-trust security assumes nothing and verifies everything—especially access and identities....
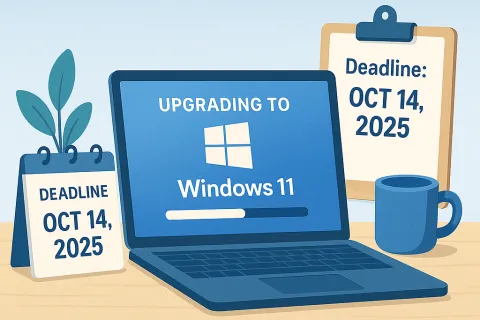
If you're still using Windows 10 on your business machines, here's the bottom line: the clock is ticking. On October 14, 2025, Microsoft will end support for Windows 10. That means no more security updates, bug...