- 1
- ...
- 13

Do you remember blowing into Nintendo cartridges to get them working? That was our version of IT troubleshooting. If a cartridge wouldn't load, we blew on it. If that didn't work, we blew harder. And if it...

How Palm Desert Businesses Can Build a Cybersecurity Strategy That Actually Works Cybersecurity has become one of the most important responsibilities for modern businesses. Companies rely on technology for...

While spring cleaning often focuses on closets, many businesses face a heavier kind of clutter beyond just a storage rack. It might be tangled up in server racks, piled in storage rooms or tucked away in back...

The Rise of Business Email Compromise (BEC) Attacks: How Cybercriminals Are Raiding Business Bank Accounts Business email compromise attacks aren't making headlines the way ransomware does, but they're quietly...
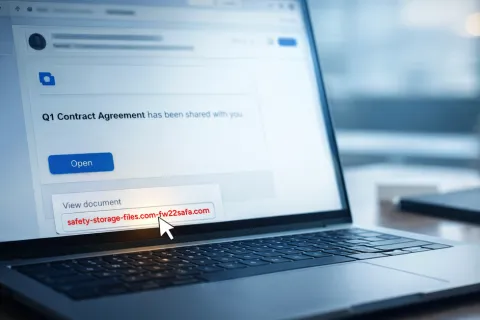
The buzz of April Fools Day fades quickly, along with its harmless pranks and fake news. Sadly, scammers keep working nonstop. Springtime marks a peak season for cyberattacks — not because workers slip...

Many business owners assume cyber attacks only happen to large corporations with massive amounts of data. In reality, small and midsize businesses are some of the most frequent targets of cybercrime. Attackers...

OT Network Segmentation — Blog Teaser :root { --navy: #1e2a3a; --orange: #e8604a; --text: #333333; --text-muted: #666666; --border: #e2e6ea; ...
Protecting Microsoft 365 and Other Communication Assets | Southwest Networks :root { --navy: #1e2a3a; --navy-dark: #151f2d; --orange: #e8604a; ...
It's early Monday morning. Coffee ready. Laptop powered on. You're set to dive into your tasks. But then, your elbow nudges the mug. Time seems to pause just long enough to watch coffee spill over the keyboard,...