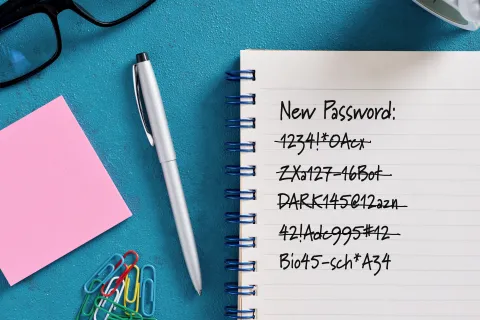
As a Level 3 Support Engineer, I frequently receive questions about security, particularly concerning password management. Users often manage passwords for multiple systems, each with different complexity...

Chatbots such as ChatGPT, Gemini, Microsoft Copilot, and the newly launched DeepSeek have transformed our interactions with technology, providing support for a wide range of tasks—from composing emails and...

Having worked in IT for over 20 years, one thing that remains constant is the need for strong policies to mitigate evolving threats. While "paperwork" is often associated with bureaucracy, in cybersecurity,...
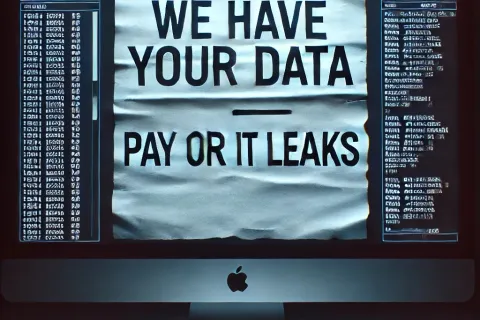
Think ransomware is your worst nightmare? Think again. Hackers have discovered a new method to hold your business hostage, and it may be even more ruthless than traditional encryption. This tactic, known as data...

We all know the classic song by The Byrds, "Turn! Turn! Turn!"—a song about the inevitability of change. This principle applies not only to life but also to IT infrastructure, particularly when it comes to software...

Mark your calendars: October 14, 2025 - the date when Windows 10 officially reaches its end of life. After this date, Microsoft will stop providing security updates, bug fixes, or technical support for Windows 10....
Before March 2020, remote work was limited to a small subset of salaried employees who had company-issued laptops. Security considerations were minimal, and traditional remote access methods, such as Remote Desktop...

When it comes to running a business, most owners focus on elements like quality customer service, dependable products or services, and carefully monitored profit and loss statements as key factors in their company's...

Business e-mail compromise (BEC) is rapidly emerging as a significant cyber threat to businesses. Although these scams have been a concern for years, the advent of advanced AI tools has made them more sophisticated...